Open-Source Budgeting: Why Transparency Matters for Your Money
Discover why open-source budgeting apps provide unmatched transparency and security for your financial data.
Discover why open-source budgeting apps provide unmatched transparency and security for your financial data.
When you hand over your financial data to an app, you’re trusting it with some of the most sensitive information about your life. Your spending patterns reveal where you live, where you work, what you eat, your health conditions, your relationships, and countless other intimate details. Yet most people have no idea what happens to this data once it enters their budget app.
This is the black box problem of modern financial software. You input your transactions, and somewhere inside a proprietary system, things happen. What things? You’ll never know. The code is locked away, the data flows are hidden, and the company’s promises are the only thing standing between your financial life and potential misuse.
Open-source budgeting apps offer a fundamentally different approach. When the code is public, everything changes. Security researchers can verify claims. Privacy advocates can audit data handling. And you, as a user, can trust not because a company asks you to, but because the evidence is right there for anyone to examine.
Most budget and expense tracking apps operate as black boxes. You download an app, create an account, link your bank, and start tracking expenses. The interface is polished, the features are helpful, and everything seems fine. But beneath that friendly surface lies a system you cannot inspect, verify, or truly understand.
When you use a closed-source financial app, you have no way to verify what actually happens to your data. The company might claim your information is encrypted, stored securely, and never shared. But how do you know? Their privacy policy is a legal document written by lawyers, not a technical specification you can verify against actual code.
Consider what a typical budget app knows about you:
This is an extraordinarily detailed financial portrait. With closed-source software, you’re trusting that portrait to remain private based solely on corporate promises and legal agreements that can change at any time.
Many apps collect far more data than users realize. Analytics platforms, crash reporting services, advertising SDKs, and third-party integrations often run silently in the background. Each of these systems may be collecting and transmitting data about your usage patterns, device information, and potentially even your financial activities.
With closed-source apps, you cannot determine:
The app might be sending your transaction data to a third-party analytics service for “product improvement.” It might be fingerprinting your device and linking your financial behavior to advertising profiles. You would never know, because you cannot see the code.
Security through obscurity is a flawed concept that persists in closed-source software. Companies claim their systems are secure, but security researchers cannot examine the code to verify those claims. Vulnerabilities may exist for years before they’re discovered through a breach rather than through proactive auditing.
Closed-source financial apps often make security claims that sound impressive but are impossible to verify:
Without access to the source code, these claims are marketing copy, not verifiable facts.
Open-source software inverts the traditional security model. Instead of hiding code and hoping nobody finds vulnerabilities, open-source projects expose everything to scrutiny. This transparency creates a fundamentally stronger security posture.
When source code is public, anyone with the relevant expertise can examine it. Security researchers, privacy advocates, concerned users, and professional auditors can all review the code for potential issues. This distributed auditing creates multiple layers of oversight that closed-source companies simply cannot match.
The open-source security community includes:
Each of these groups brings different perspectives, skills, and motivations. A privacy researcher might notice data collection patterns that a security auditor overlooks. A developer integrating with the project might discover edge cases the original authors missed. This diversity of attention is a strength no single security team can replicate.
When vulnerabilities are discovered in open-source software, the path from discovery to fix is typically faster and more transparent than in closed-source alternatives. Security researchers can:
Compare this to closed-source software, where researchers often cannot even verify whether a vulnerability they reported was actually fixed. They have to trust the vendor’s word, which history has shown is not always reliable.
The security principle that open-source embraces is simple: assume your adversaries can see your code and design security that works anyway. This leads to fundamentally stronger security architectures:
When you cannot hide your implementation, you have to get it right. This pressure produces better security outcomes than the false comfort of hidden code.
You don’t need to be a programmer to evaluate the trustworthiness of an open-source project. While you may not be able to review code line by line, you can assess many important factors that indicate whether a project deserves your trust.
Every well-maintained open-source project has an issue tracker where bugs, feature requests, and concerns are discussed. This is a goldmine of information about how the project operates:
What to look for:
A project that ignores security issues or dismisses user concerns is sending clear signals about its priorities. Conversely, a project with thoughtful, timely responses to concerns demonstrates genuine commitment to its users.
Professional security audits are a significant investment that demonstrates a project’s commitment to security. Look for:
The absence of professional audits isn’t necessarily disqualifying, especially for smaller projects. But for apps handling sensitive financial data, some form of external security validation is reassuring.
Modern software depends on many external libraries and frameworks. An app might have excellent code internally while relying on problematic dependencies. You can evaluate dependency health by looking at:
Tools like GitHub’s dependency graph and security advisories make this information visible even to non-technical users. A project with dozens of outdated dependencies and unaddressed security warnings should raise concerns.
One of the most powerful aspects of open-source software is the ability to verify privacy claims against actual implementation. While you may not be able to read code yourself, you can look for:
Communities around privacy-focused open-source software often include members who specifically audit data flows and report their findings. Their analyses can help you understand what the code actually does.
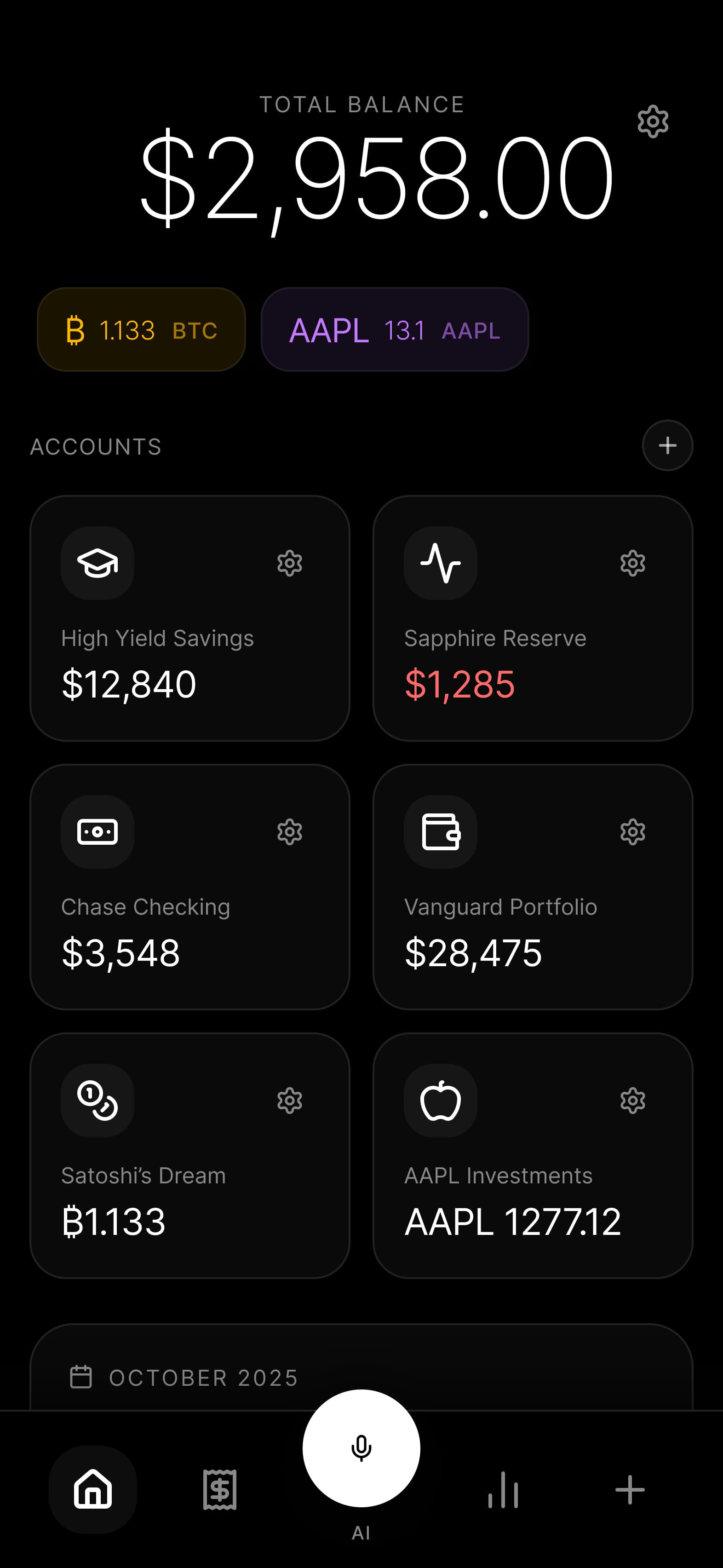
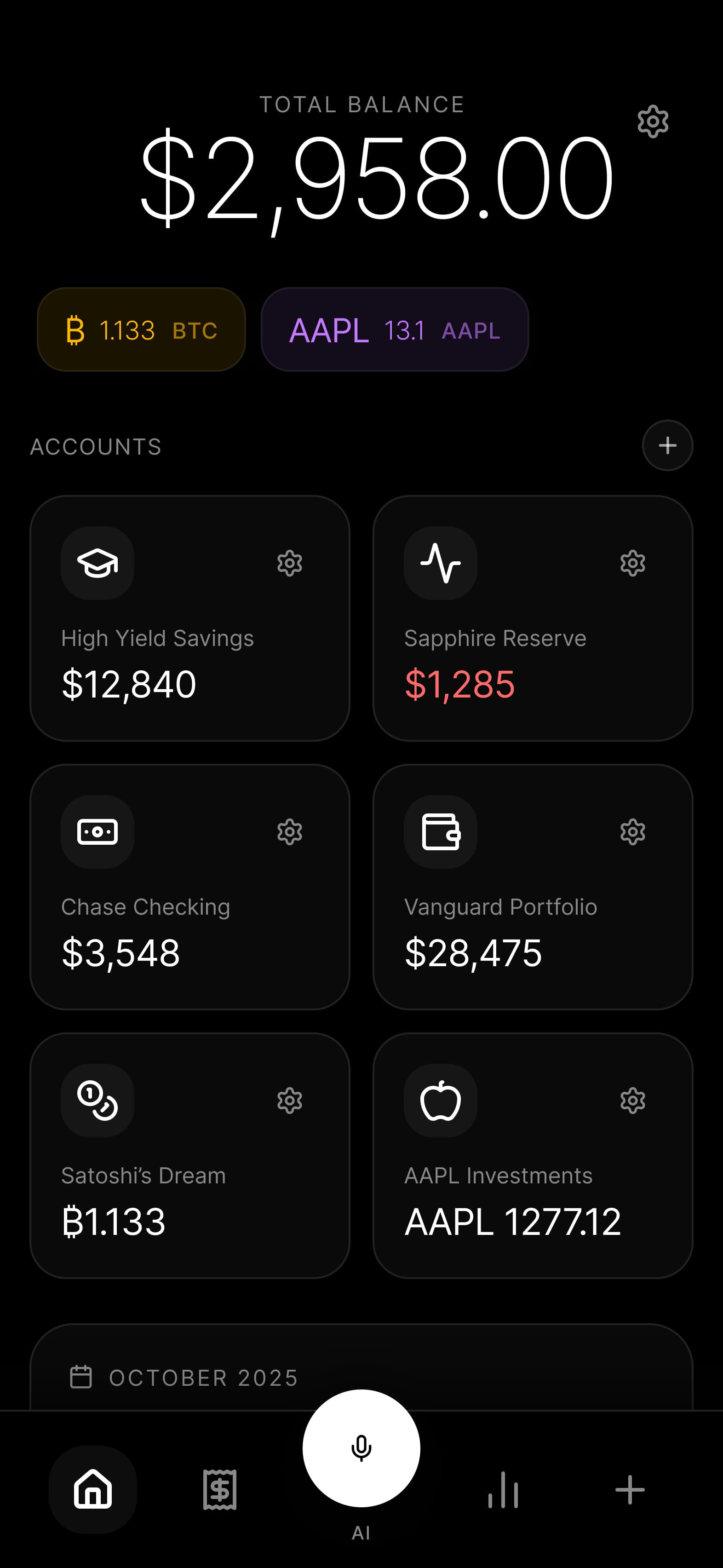
Budgie is built on the principle that you shouldn’t have to trust us. You should be able to verify our claims, examine our code, and confirm that we do what we say. Everything about Budgie is open source, from the mobile app to the backend services.
Unlike some projects that open-source only portions of their code while keeping critical components proprietary, Budgie is 100% open source:
This complete transparency means there are no hidden components where concerning behavior could hide. Every line of code that touches your data is available for examination.
Budgie uses the MIT License, one of the most permissive open-source licenses available. We chose this license for several reasons:
For users:
For the community:
We believe that restrictive licensing undermines the trust benefits of open source. If you cannot freely examine and share the code, the transparency is incomplete.
Open source thrives on community participation. If you want to contribute to Budgie, there are many ways to get involved:
For developers:
For non-developers:
For security researchers:
Visit our GitHub repository to get started.
An open-source project is more than just public code. It’s a community of users, contributors, and maintainers working together toward shared goals. How that community is governed matters for the project’s long-term health and trustworthiness.
Budgie follows a transparent decision-making process:
Feature decisions:
Security decisions:
Privacy decisions:
Our development roadmap is public and regularly updated. You can see:
This transparency lets you make informed decisions about whether Budgie is right for you. If a planned feature concerns you, you can raise those concerns before it’s implemented. If a feature you need is missing, you can advocate for it or contribute it yourself.
We take security vulnerabilities seriously and have established processes for responsible disclosure:
For security researchers:
Our commitments:
We believe that welcoming security research makes Budgie safer for everyone. Researchers who examine our code are doing us and our users a service.
Budgie isn’t the only open-source option for financial management. A healthy ecosystem of alternatives exists, and we believe in acknowledging them fairly. Different tools suit different needs, and the best choice depends on your specific requirements.
Actual is a privacy-focused budgeting tool with a strong local-first approach. It offers envelope budgeting methodology, bank syncing capabilities, and both self-hosted and cloud options. If you prefer envelope-style budgeting and want a desktop-focused experience, Actual is worth considering.
Firefly III is a comprehensive personal finance manager designed for self-hosting. It offers detailed transaction tracking, budgeting features, and extensive reporting. If you’re comfortable managing your own server infrastructure and want maximum control, Firefly III provides powerful capabilities.
GnuCash is a veteran of open-source finance software, offering double-entry accounting suitable for personal and small business use. If you need accounting-grade features like invoicing and business expense tracking, GnuCash’s mature codebase has decades of development behind it.
Budgie focuses specifically on mobile-first, offline-first expense tracking. Our priorities are:
We think there’s room in the ecosystem for all these tools. Users benefit when they have choices, and competition among open-source projects drives innovation while maintaining the trust benefits of transparency.
Open-source software isn’t automatically more secure, but it enables better security through transparency. When code is public, security flaws can be found and fixed by anyone with the expertise, not just the original developers. This distributed scrutiny typically catches problems faster than relying solely on internal security teams. However, the security benefits only materialize when the community actually reviews the code, so active, well-maintained projects are more likely to be secure than abandoned ones.
This is a common concern, but security research consistently shows that obscurity provides weak protection. Determined attackers can reverse-engineer closed-source applications, find vulnerabilities through fuzzing and probing, or exploit the same bugs that internal developers missed. Meanwhile, legitimate security researchers are blocked from helping. Open source assumes adversaries will study the code and designs security that works anyway. This produces more robust systems than hoping attackers won’t look too closely.
This is a valid concern known as “build verification.” Budgie uses reproducible builds where possible, allowing anyone to verify that the published app matches the source code. For mobile apps, additional trust is required in the app store distribution, but the open-source code ensures you can build the app yourself if you want maximum verification. We also provide checksums for releases so you can verify download integrity.
One of the key benefits of open-source and offline-first architecture is data sovereignty. Your data is stored locally on your device, not locked in some company’s cloud that might disappear. If Budgie development stopped tomorrow, your data would still be on your phone, and the open-source code would allow anyone to continue development or create export tools. You’re never locked in.
No. While anyone can propose changes to the code, you control which version you run. Updates only install when you choose to update the app. If you’re concerned about a particular version, you can review the changes before updating or even build your own version from source. The open nature of the code means changes are visible and reviewable, actually giving you more control rather than less.
Budgie is free to use with optional premium features for users who want additional capabilities. Our business model relies on users who find enough value in the product to support its development, not on monetizing user data. The open-source nature actually supports this model because users can trust their data isn’t being sold, making them more willing to pay for premium features. Transparency and sustainable business can coexist.
Financial software that respects your privacy shouldn’t require blind faith. When you choose an open-source budget app, you’re choosing verifiable security over marketing promises. You’re choosing community oversight over corporate opacity. You’re choosing to trust evidence rather than assertions.
Budgie embodies this transparent approach. Every line of code is public. Every decision is documented. Every claim is verifiable. We don’t ask you to trust us because we say so. We ask you to trust us because you can see exactly what we do.
Your financial data deserves this level of transparency. The patterns in your spending reveal intimate details about your life, and you have every right to know exactly how that information is handled. Open-source budgeting makes that knowledge possible.
Ready to experience financial tracking built on transparency? Explore our open-source code, learn about our security practices, and join the waitlist to be among the first to use Budgie. Your money. Your data. Your ability to verify every claim we make.
2025-02-10
A technical deep-dive into Budgie's offline-first architecture, explaining how SQLite, AES-256 encryption, and device-to-device sync keep your financial data completely private.
Read article→2025-01-29
Explore the local-first movement, CRDTs, sync engines, and why developers are choosing offline-first architecture for privacy-sensitive applications.
Read article→Join the Budgie waitlist and be the first to experience truly private expense tracking.
Join Waitlist