Why Cloud Budgeting Apps Are a Privacy Nightmare
Discover the hidden privacy risks of cloud-based budgeting apps and learn why offline-first architecture is the safer alternative for your financial data.
Discover the hidden privacy risks of cloud-based budgeting apps and learn why offline-first architecture is the safer alternative for your financial data.
You track every coffee, every subscription, every paycheck. Your budgeting app knows more about your life than your closest friends. It knows where you eat, what you buy, when you get paid, and how much debt you carry. Now consider this: that data sits on servers you do not control, managed by companies whose primary business model depends on monetizing user data.
This is not hypothetical risk assessment. This is the reality of cloud-based personal finance applications in 2025.
The personal finance app market has exploded. Mint, YNAB, Copilot, Monarch Money, Lunch Money, and dozens of others promise to help you manage your money. Most offer free tiers or low monthly subscriptions that seem reasonable for the value provided.
Here is the first question every IT professional should ask: How does a company offering a free service that requires significant infrastructure, development resources, and regulatory compliance make money?
The answer varies by company, but the patterns are consistent:
None of these revenue models work without collecting, analyzing, and retaining your financial data. Your transaction history is not just a feature of the product. It is the product.
When you connect a bank account to a cloud budgeting app, your single bank connection creates copies of your data across multiple systems, each with different security postures, retention policies, and access controls. Your data flows from your bank account through a data aggregator like Plaid, Yodlee, MX, or Finicity, into the aggregator’s data warehouse, and then into the budgeting app’s backend. From there, it may feed into analytics pipelines, ML/AI training data, and third-party analytics services. The attack surface is not your bank. It is every system in this chain.
Understanding the technical mechanisms of data collection reveals why cloud-based financial apps pose inherent privacy risks.
Plaid dominates the financial data aggregation market. When you see a login screen for your bank inside a budgeting app, Plaid is usually behind it. Here is what Plaid collects:
Plaid’s privacy policy explicitly states they retain this data and may use it for product improvement, analytics, and to develop new services. When you connect your bank through Plaid, you are not just sharing data with the budgeting app. You are sharing it with Plaid, which operates as a separate data controller.
In 2022, Plaid settled a $58 million class action lawsuit over allegations that they collected more data than users authorized and retained it longer than necessary. The settlement included claims that Plaid obtained login credentials through interfaces designed to look like bank login pages, leading users to believe they were logging directly into their banks.
Before API-based aggregation, apps used screen scraping: automated systems that log into your bank with your credentials and parse the HTML of your account pages. This method is still used when banks do not support API access.
The security implications are severe:
Screen scraping means a third party can do anything you can do in your bank account. They choose not to, but the technical capability exists.
Open Banking regulations in the EU and UK, along with voluntary API programs from US banks, enable more controlled data sharing. Apps request specific scopes of access, and you authorize through your bank’s interface.
This is more secure than screen scraping, but privacy concerns remain:
This is not theoretical. Financial apps have been breached, and user data has been exposed.
In December 2023, Intuit announced they were shutting down Mint after 17 years. Users were given 90 days to export their data before it was deleted. This raises several concerns:
When a company shuts down, the data does not necessarily disappear. It often becomes an asset sold to the acquiring company or retained in archives with unclear access policies.
Block, the parent company of Cash App, disclosed that a former employee downloaded internal reports containing customer data for over 8 million users. The breach included full names, brokerage account numbers, portfolio values, and stock trading activity.
This breach illustrates insider threat risk. No external hacker was involved. An employee with legitimate access chose to exfiltrate data. Cloud systems with centralized data stores are inherently vulnerable to this attack vector.
Beyond the 2022 settlement, Plaid has faced ongoing scrutiny:
When you connect through Plaid, you enter into a relationship with Plaid, not just the app. Plaid’s business interests may not align with your privacy preferences.
Envestnet Yodlee, another major data aggregator, faced FTC action for allegedly selling detailed financial data that could be used to identify individuals. The data included transaction-level information that, combined with other data sources, enabled detailed consumer profiling.
The lifecycle of your financial data extends far beyond your active use of an app.
When a fintech company is acquired, user data is typically the most valuable asset. Consider what happens:
You agreed to one company’s privacy policy. After acquisition, a different company with different policies controls your data. The legal basis for this is usually buried in the original terms of service.
When companies fail, data handling varies:
Fintech companies operate in a volatile market. The app you trust today may not exist in two years.
Even if you delete your account with a budgeting app, the aggregator (Plaid, Yodlee, etc.) may retain your data. You have a relationship with the app and a separate relationship with the aggregator. Deleting one does not necessarily affect the other.
To fully disconnect, you must:
Most users never complete step 3 or 4.
Plaid deserves focused analysis because of its market dominance. Over 12,000 apps use Plaid, connecting to 12,000+ financial institutions. If you use fintech products, you almost certainly have data in Plaid’s systems.
When you connect through Plaid, the consent flow works like this:
The consent you provide to the app does not limit what Plaid collects. Plaid’s systems pull comprehensive data, and the app requests subsets through the API. The delta between what Plaid collects and what the app needs sits in Plaid’s infrastructure.
Plaid’s privacy policy allows data retention even after you disconnect:
That last point is significant. Your data, in aggregate form, may inform products you never agreed to.
Plaid started as infrastructure for fintech apps. It has evolved into:
Your transaction data contributes to products sold to landlords evaluating rental applications, lenders assessing loan risk, and employers verifying income claims. The infrastructure provider became a data company.
If you must use a cloud-based financial app, here is a technical checklist for evaluation.
The privacy problems outlined above share a root cause: centralized data storage on servers you do not control. Offline-first architecture eliminates this attack vector entirely.
In an offline-first application:
The server cannot be breached because there is no server. Employee access is impossible because there are no employees with access to your data. Data aggregators are not involved because there is no aggregation.
Offline-first does not mean you cannot sync with banks. It means the sync architecture protects your privacy. With traditional cloud sync, your data flows from your device to a cloud server, then to an aggregator, and finally to the bank, with databases at each step. With offline-first sync, bank data flows directly to your device through a secure proxy and is stored only in your local database.
With offline-first, bank data flows directly to your device. No intermediate servers store your transactions. No aggregators retain your history.
Offline-first architecture involves tradeoffs:
For users who prioritize privacy, these tradeoffs are acceptable. Your financial data is too sensitive to trust to companies whose incentives may not align with your interests.
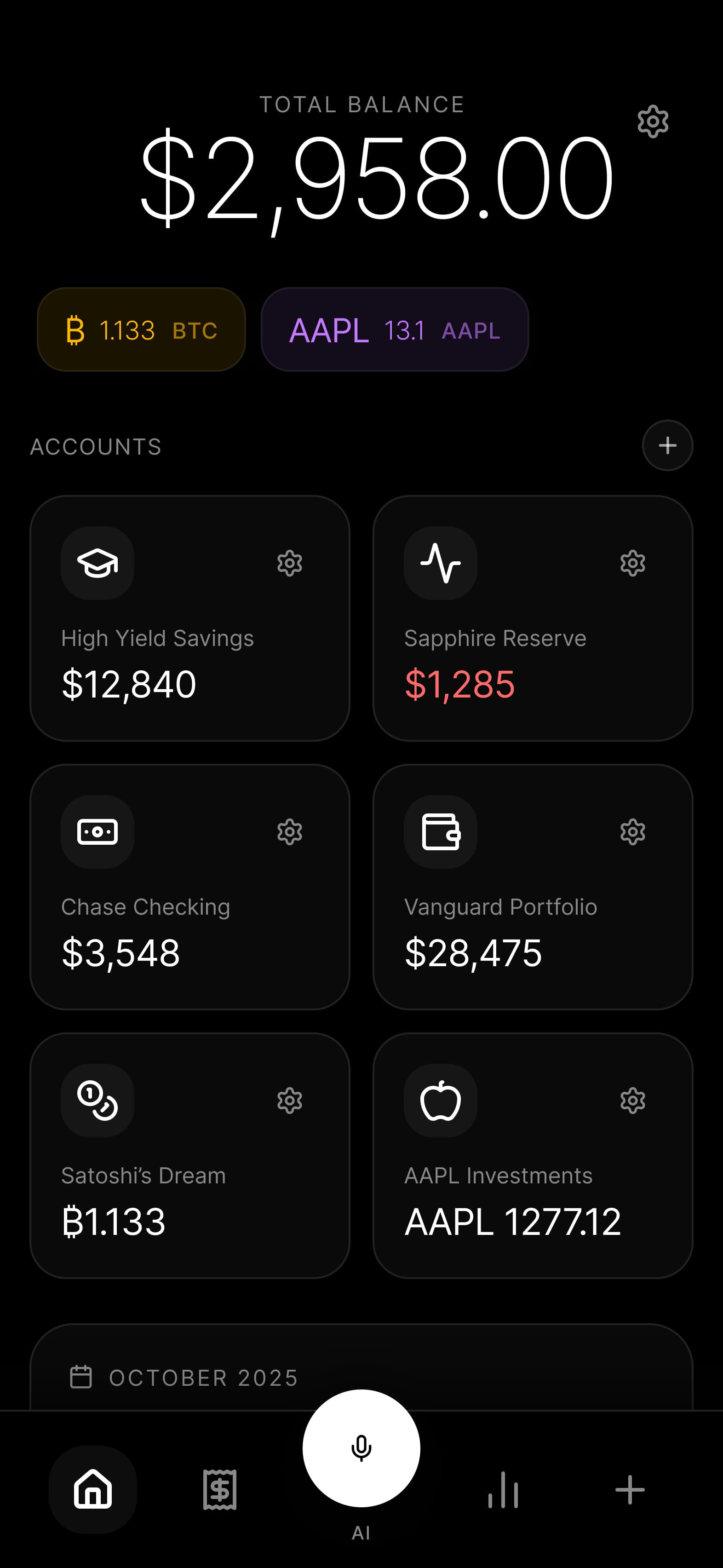
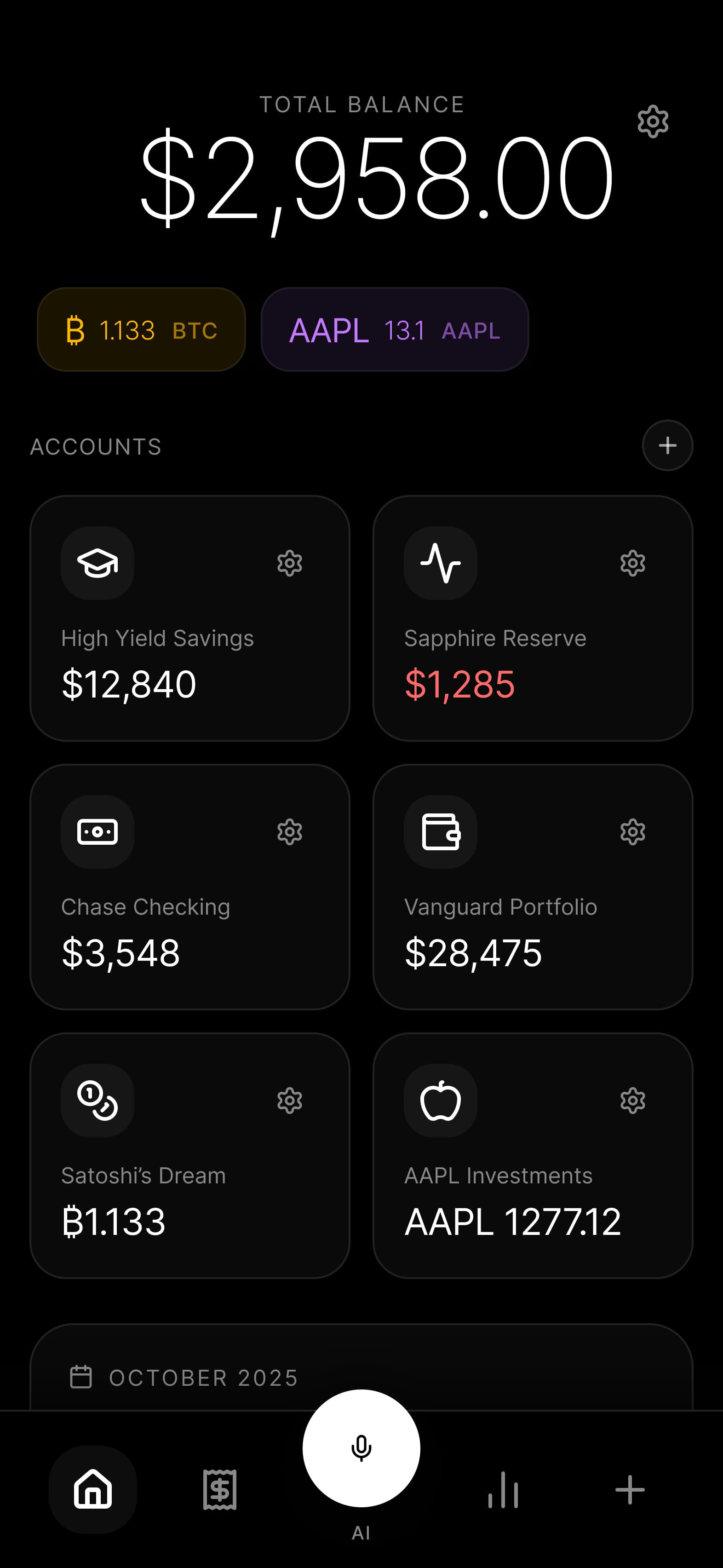
Budgie implements offline-first architecture with no compromises:
The security architecture is designed for users who understand the risks described in this article and want an alternative.
If you currently use cloud-based financial apps, here are concrete steps to reduce your exposure.
Yes, with consent. When you agree to terms of service and privacy policies, you typically grant broad data collection and sharing rights. The legal framework in most jurisdictions allows extensive data use if disclosed in policies most users never read. GDPR in Europe provides stronger protections, including data minimization requirements, but enforcement varies. In the US, financial data protection is fragmented across state laws with no comprehensive federal standard.
You can request deletion, and under CCPA (California) and GDPR (Europe), companies must comply. However, there are exceptions for compliance, fraud prevention, and legitimate business interests that can justify retention. The process typically requires contacting each aggregator directly, not just the app you used. Plaid provides a portal at my.plaid.com for viewing and managing connections. Full deletion verification is difficult to confirm.
Open banking APIs are significantly safer than screen scraping. APIs provide granular consent, limited scopes, and no credential sharing. However, privacy concerns remain because aggregators still collect and retain data, and apps often request more access than necessary. Open banking solves security problems (credential theft, session hijacking) but does not solve privacy problems (data aggregation, retention, secondary use).
True end-to-end encryption would prevent the provider from accessing your data, but most cloud budgeting apps claiming encryption use encryption in transit and at rest, not end-to-end. They can still access your data because they hold the keys. Apps with true end-to-end encryption lose functionality (server-side categorization, web access, shared budgets) that most cloud apps offer, which suggests their encryption claims may not cover all data.
Budgie’s bank sync uses direct connections to bank APIs where available, bypassing data aggregators entirely. Credentials are stored locally on your device with hardware-backed encryption, not on any server. Transaction data flows directly from your bank to your device without intermediate storage. In regions where direct API access is not available, manual import from bank exports provides a fully private alternative.
Nothing happens to your data because Budgie does not have your data. Everything is stored locally on your device. If Budgie as a company ceased to exist, your app would continue to function with all your data intact. You can export data at any time in standard formats. There is no server to shut down, no migration to worry about, no acquisition that could change data handling. Your data remains yours permanently.
Cloud budgeting apps solve a real problem, but they solve it in a way that creates new problems. The convenience of automatic transaction import, AI categorization, and cross-device sync comes at the cost of your financial privacy.
For IT professionals who understand these tradeoffs, offline-first architecture offers a path forward. Your financial data deserves the same security posture you would apply to production credentials or customer data.
Ready to take control of your financial data? Join the Budgie waitlist and experience truly private expense tracking.
2025-02-10
A technical deep-dive into Budgie's offline-first architecture, explaining how SQLite, AES-256 encryption, and device-to-device sync keep your financial data completely private.
Read article→2025-11-06
Discover why offline-first architecture is the only truly private approach for financial apps. Learn about data risks, privacy by design, and how Budgie keeps your finances secure.
Read article→Join the Budgie waitlist and be the first to experience truly private expense tracking.
Join Waitlist