Most personal finance apps that offer bank synchronization rely on a financial data aggregator to make it work. The aggregator sits between you and your bank, collects your credentials or OAuth tokens, and feeds transaction data back to the app. This pattern is so common that many users assume it is the only way automatic bank sync can work.
It is not. And the aggregator pattern carries risks that are rarely disclosed clearly to users. This article explains what aggregators do, why mass aggregation creates a high-value breach target, and how an offline-first architecture provides a structurally safer alternative.
The Aggregator Pattern: What Plaid Does and What It Sees
Plaid is a financial-data aggregator that acts as an intermediary between consumer finance apps and banks. When you connect a bank account through an app that uses Plaid, here is what happens at the data layer:
- Credential collection — For banks that do not support direct OAuth, Plaid historically used screen-scraping, which required your actual username and password. Many integrations have migrated to OAuth tokens, but the credential handling still flows through Plaid infrastructure.
- Transaction mirroring — Plaid pulls your transaction stream from the bank and stores it. The aggregator holds a copy of your financial history on its servers, separate from the app you are actually using.
- Data sharing — Plaid data can be shared with other Plaid-connected apps you have previously authorized, lenders, credit bureaus, and partners under terms that users rarely read in full.
- Retention — Transaction data is retained beyond the active period of any individual app connection. Deleting the app does not automatically delete the data from the aggregator.
This means that when you use any budgeting app backed by a major aggregator, your bank data exists in at least three places: your bank, the app, and the aggregator. Each is an independent breach surface.
Why Mass Aggregation Is a High-Value Breach Target
A financial data aggregator that services millions of users holds credentials or access tokens for millions of bank accounts in one system. From an attacker perspective, this is a far more attractive target than any individual bank, because:
- Single point of entry — Compromising one system yields access to credentials spanning hundreds of different banks and financial institutions. Attackers do not need to target each bank individually.
- Concentrated transaction history — Aggregators hold not just credentials but also years of normalized transaction history. This data is valuable for identity fraud, account takeover, and social engineering attacks.
- Third-party security posture — A major aggregator security posture is determined by that company, not by your bank. Your bank may have excellent security practices, but your data exposure now depends on a third party you did not explicitly choose.
This risk is not theoretical. Major financial data aggregators and fintech intermediaries have experienced significant security incidents over the years, exposing consumer banking credentials, account numbers, and transaction history. Each incident affected users of multiple apps simultaneously, because the breach was at the aggregator layer rather than any individual application.
Offline-First as the Architectural Answer
An offline-first architecture addresses aggregator risk at the structural level rather than through policy promises. When your financial data is stored on your device and bank sync happens directly — without an intermediary — the aggregator attack surface does not exist.
What Changes Architecturally
- No credential escrow — Your bank credentials or OAuth tokens are stored only on your device, encrypted at rest. No third-party server holds a copy.
- Direct bank communication — When sync runs, your device communicates directly with your bank API. The transaction data flows from bank to device without passing through an intermediary server.
- No aggregator copy of your history — Because sync is direct, there is no second copy of your transaction stream on an aggregator server. The only copies are at your bank and on your device.
- Breach impact is isolated — If your device is compromised, the exposure is limited to your accounts. An aggregator breach can expose every user simultaneously.
Direct API Tokens vs Aggregator OAuth
Many banks now offer official API programs with scoped OAuth tokens. These tokens grant read-only access to transaction history without exposing login credentials. When used in an offline-first app, this is the most secure form of automated bank sync available:
- Scoped permissions — The token grants access only to transaction data. It cannot initiate transfers, change account details, or access other banking services.
- Revocable — You can revoke the token from your bank portal at any time, immediately terminating access without changing your password.
- No credential exposure — The token is generated by your bank, not derived from your password. Even if the token is intercepted, your login credentials remain safe.
- Stored locally — In an offline-first app, the token lives on your device, not on an aggregator server. Revoking it from your bank also removes the only remaining access path.
Aggregator OAuth, by contrast, routes your bank authorization through the aggregator platform. The resulting token is held by the aggregator, not by the app or your device. You are trusting the aggregator to use it responsibly and to secure it adequately.
PDF, Excel, and CSV Imports as the Universal Fallback
Not every bank offers an API program, and not every bank is supported by a given direct-sync integration. For these cases, manual statement import is the privacy-preserving fallback — and it is more practical than most people expect.
Why Manual Import Is Underrated
- Universal compatibility — Every bank that has ever existed can produce a statement. CSV and PDF exports work with every financial institution on the planet, with no API access required.
- No ongoing credential exposure — You download a statement from your bank website using your normal login, then import the file. There are no tokens, no saved credentials, and no persistent connection to manage.
- Predictable frequency — Most users reconcile their accounts weekly or monthly. Manual statement import fits naturally into this cadence without requiring always-on connectivity.
- Audit trail control — You decide exactly which time periods to import. There is no background sync pulling in data without your explicit action.
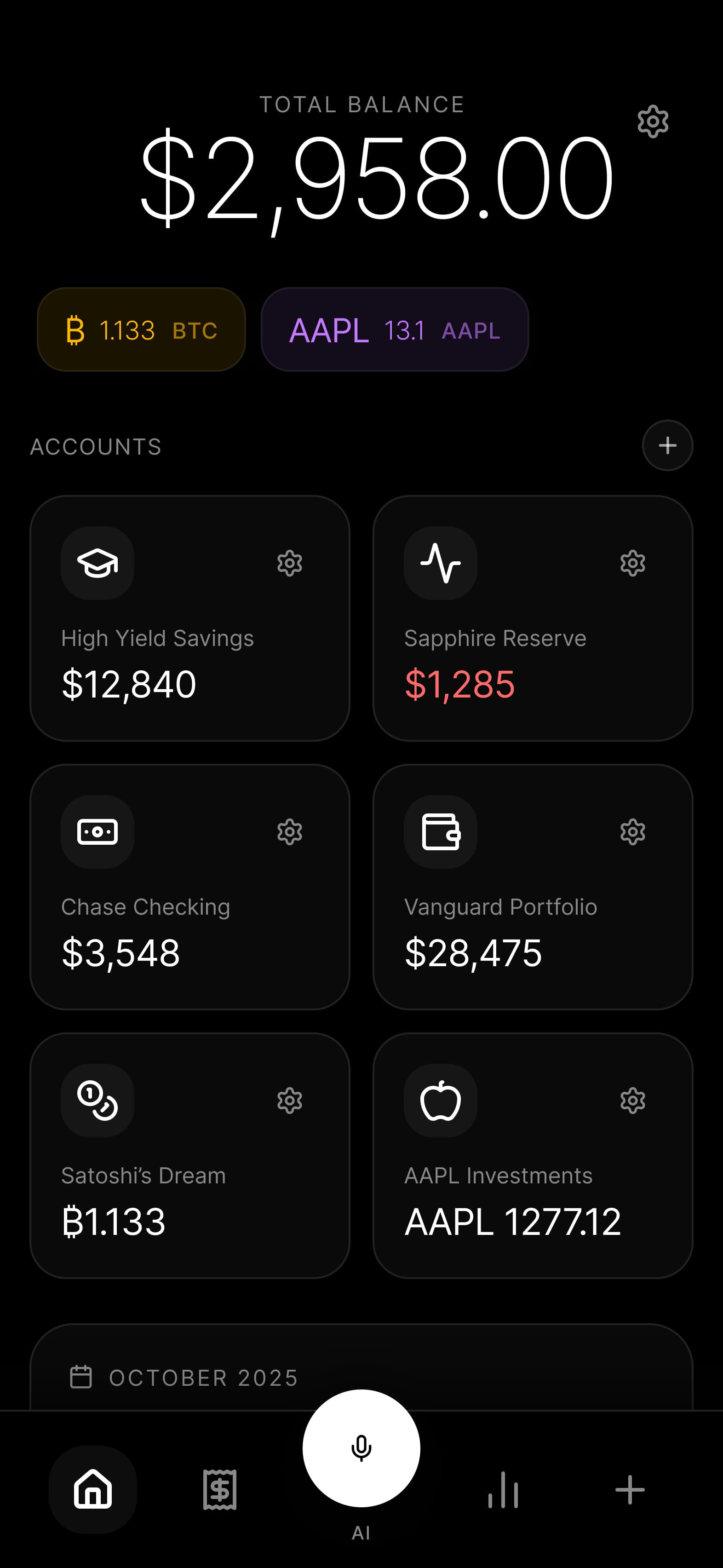
How Budgie Implements This End to End
Budgie supports both direct bank sync and manual import, with a consistent commitment to keeping your data on your device at every stage.
Direct Sync
For supported banks, Budgie connects directly from your device to the bank API using OAuth tokens stored in the encrypted local database. The sync runs on your device; Budgie servers are not involved in the data flow. Transaction data is written directly to the local SQLite database.
CSV and PDF Import
Budgie CSV and PDF import parses statement files on your device. No file content is uploaded to any server during import. The parser runs locally, extracts transactions, and writes them to the local database. Deduplication ensures that importing overlapping date ranges does not create duplicate records.
Encrypted Local Storage
Whether data arrives via direct sync or manual import, it is stored in the same AES-256 encrypted SQLite database. The database is protected by your device PIN, biometric authentication, or a dedicated app lock. No transaction data is stored on Budgie servers at any point.
Encrypted Backup
When you create a backup, the encrypted database file is exported to your chosen destination — iCloud, Google Drive, a local network share, or a USB-connected device. Budgie does not receive or store the backup. Restoration reads the file from the same destination and decrypts it locally.
Frequently Asked Questions
Does Budgie use Plaid for bank sync?
No. Budgie bank sync connects directly from your device to supported bank APIs without routing through a financial aggregator. For banks not yet supported by direct sync, CSV and PDF import provides full compatibility without any third-party credential handling.
Is CSV import really secure enough for ongoing use?
Yes, for most users. Manual import aligns naturally with how people actually review their finances — weekly or monthly. The security advantage is significant: there are no stored credentials, no persistent connections, and no third-party services involved. Many security-conscious users prefer this model precisely because it is explicit and auditable.
What if my bank requires an aggregator for the app I currently use?
Switching to Budgie CSV import eliminates the aggregator entirely. Download your statement from your bank website as you normally would and import it into Budgie. You gain full transaction history without any ongoing credential exposure to a third party.
How does Budgie handle OAuth tokens for direct sync?
OAuth tokens for direct bank sync are stored in the encrypted local database on your device alongside your transaction data. They are protected by the same AES-256 encryption and device authentication as your financial records. Revoking a token from your bank portal immediately terminates all sync access without requiring any action inside Budgie.
Can I verify that Budgie does not send my bank data to a server?
Yes. Budgie is open source. You can review the bank sync and import code to confirm that no outbound calls send transaction data to Budgie servers. The network requests during sync go directly from your device to your bank API endpoint.